Over the past two months, I have been asking myself and my social networks the same question.
The answers I have sought to uncover were masked by partisan politics and moral indecision. Following the advice of Richard Ledgett (of the NSA) I continued to learn and dig into the facts about Internet and Cyber Privacy. What I found, and what I learned, opened my eyes to a world that I had never seen before – the world of digital warfare.
We All Need a Mentor
At my first teaching job, I worked with “At-Risk” High School Students in Colorado. It was an eye-opener in a number of ways, but the most striking for me, was the lack of technical knowledge. As a teacher, and with a captive audience, I slowly started teaching my students what technology really is – the ultimate expression of democracy. To start the process, I guided my students through a short lesson on influential documents of a democratic society: The Magna Carta, The Declaration of Independence, The Constitution, The UN Charter, and… The Conscience of a Hacker (written by The Mentor in 1986). To me, and to my students, The Conscience of a Hacker was a shot at “the man” for miss-interpreting the power of the internet and the wonders of a curious mind. The Mentor wrote:
This is our world now… the world of the electron and the switch, the beauty of the baud. We make use of a service already existing without paying for what could be dirt-cheap if it wasn’t run by profiteering gluttons, and you call us criminals. We explore… and you call us criminals. We seek after knowledge… and you call us criminals. We exist without skin color, without nationality, without religious bias… and you call us criminals. You build atomic bombs, you wage wars, you murder, cheat, and lie to us and try to make us believe it’s for our own good, yet we’re the criminals.
Yes, I am a criminal. My crime is that of curiosity. My crime is that of judging people by what they say and think, not what they look like. My crime is that of outsmarting you, something that you will never forgive me for.
I am a hacker, and this is my manifesto. You may stop this individual, but you can’t stop us all… after all, we’re all alike.
If you have not seen the manifesto before, please read it! In the history of cyber literature The Conscience of a Hacker is one of the most concise expressions about the war on “Hackers.”
Since the 1980’s the term “Hacker” has become almost synonymous with “Criminal.” I am a child of 1985, I am a Technologist, I am a Hacker, and under certain conditions, I could be called a criminal. In my quest for technical knowledge, I have created viruses, hacked wireless networks, disseminated copyrighted materials, and learned more than I ever did in school. I am a member of black-listed organizations and my name and pseudonyms grace many internet rolls.
I crossed my first technology line at the age of 12, using my home computer. I was stuck behind the Pay-Wall to a website that I wanted access to (believe it or not it was for a digital copy of the Encyclopedia of Diving). It seemed like all of my searches kept pulling up cool information that I could not access. So, like Ýmir Vigfússon, I started testing the site for weaknesses. One of the pay-gates allowed for a “bank account and routing number” payment. Grabbing an image of a Checkbook, I started putting in data to see where I would get. After some trial and error, I found that I could put in a fake name, fake email, and fake account number – as long as the routing number was from an existing bank. I was in!
After about 5 minutes, the “Paranoid” chemicals hit my brain. Two minutes later, I had deleted my account, cleared my computer – and sat wondering what to do…
Using a burner email address, I emailed the webmaster of the company and told him everything that I had done. I went into extreme detail on how I broke into their system using fake data. After three agonizing days, I received a reply: “Thanks!” The webmaster attached a copy of the documents I wanted in exchange for my detailed account of how to fix his system. Ever since that day, I have always tried to stay on the right side of the hacking line (and only crossed it one more time – to save someone’s life).
In my course of learning about technology, I downloaded and purchased a wide range of resources: virus how-to guides, hardware keyloggers, advanced WiFi antenna’s, etc. I also sought to learn from the communities of online experts that freely share technical information (usually termed as Hacker Gangs). At one point in my quest, I was an acolyte in the Church of Wifi, a member of The Pirate Bay, a member of Phrack, and a member of Hacker Monthly. I characterize myself as a White-Hat – or a Hacker for Good – but the only real difference between white and black is who is observing. If I looked at my own search histories and pseudonyms, I would label myself as a pretty shady bloke.
In 2008, The Mentor was my mentor, and he helped me to see more than I thought was possible. In this age of decreasing internet privacy, who is willing to be a mentor if it means being labeled as a criminal?
Why is internet privacy important?
One of the fundamental draws of the internet has been anonymity. The ability to say what you want without censorship or monitoring. The best place to see the freedom of anonymity is by looking at a stack of comments on YouTube. Would people post those horrible things if they knew that all of their friends, coworkers, and family members would learn about it? Learning about internet privacy made me ask some important questions:
Have you ever posted something online that you don’t want anyone to know about?
Is the account you used in any-way connected to who you really are? Don’t just say no, think about it! YouTube = Google = Google+ = additional Google reviews and ratings. In a previous case of students using pseudonyms to hide online hate group affiliations, I could see – from a YouTube comment – the link to the students Google+ Profile. That profile, even though under a pseudonym, held a recent review for a business in the area (with a lot of specific information). It only took one phone call to learn who the student was. In the IT World, I am fairly capable, but so is your company IT Department, and your next companies IT Department – keep that in mind.
Now, what makes it scarier is the introduction of the cellphone. If you happened to use your personal phone for the post, your IP Address, MacAddress, Routing Information, and GPS Coordinates are contained in the post data! So not only do I know who you are, I know where you live, and what type of phone you carry. In his Ted Talk, James Lyne explains how most images are encoded with GPS data by default. Think of that in terms of online dating profiles – your profile photo is engraved with the location where you took it (probably your home). When I teach students about the scary side of the internet, I caution them that 3 pieces of information is all it takes to find you – if you post a GPS located photo of yourself, you’ve been found!
Have you ever searched for something that you did not want to ask a real person?
We all have! From “what should I do if…” statements to “how do I…” queries, our entire life is in our internet history. Some security analysts say that Google has become our most trusted confidant. We ask it questions that we would never ask anyone face to face. But, if you happen to be signed into YouTube, Facebook, Twitter, Google, etc. when you make that query, Google – and everyone with access to Google – knows your most dirty secrets. On the other hand, do you want to be able to search for something outside of your own sphere? Do you want to reach a result that does not conform to your current view? Good Luck! In a recent Ted Talk, Eli Pariser quoted an unknown Google Engineer who explained that Google Search uses 57 identifying characteristics – even when you are not signed in – to tailor your search results (which is probably why I had a very hard time finding Anti-Snowden stories). Just think about that… If I search now, from a Mac in South Korea, I will not get the same search results as a friend on a PC in Colorado.
Have you ever downloaded something that you shouldn’t?
In some documents released by Snowden, the NSA listed two priority website targets: The Silk Road, and The Pirate Bay. If you are a torrenter – you’re probably hosed.
I am proud and humbled to say a resounding “YES” to all of the questions above. If you also answered yes to one or more of those questions, it means that everything you do online is tied to who you are – the internet is no-longer nationless, genderless, or borderless.
Learning Abroad
Since I currently live overseas, I happen to live in a state of surveillance. As I write this, I can see directly over my monitor is a Security Camera which goes to our own “Panopticon” room in the basement (which is managed by the school “Central Control Team” – one of the most aptly named groups in our company). They are always watching… or so they want us to believe. Like it or not, we change our behavior when we know we are being watched. On another front, in my legitimate, but not necessarily kosher, internet searching, I occasionally get blocked by the Korean Government. It is nothing like in China, but it is a constant reminder that they are out there, censoring what we do and what we look at. The message is clear: I am not capable of making decisions on my own – I must be monitored.
I am a connected American who moved overseas. It was surprising how many virtual services disappeared when my physical body crossed a political border. Netflix, Hulu, HBO, Skype, Google, Spotify, and a slew of other companies started hounding me with messages saying: “We have not come to your part of the world yet.” The internet is here, like it or not Hulu is also here! I am an American, I am a citizen of the internet, and in most cases, I am paying for services that these companies provide… or did… before I found out that they geographically discriminate on a global scale. Since 1986, the internet has become a place of virtual borders and classes (Americans have more internet “privileges” than people located in other countries).
Student Privacy
In my professional world, I am an oppressor. In my role as a Technology Director, I actively seek out and destroy programs that hamper our ability to monitor students 24/7. My Predecessor setup his own digital “Panopticon” on a big-screen TV that scrolled through live images of our students’ computer screens. When a student was discovered breaking our “Acceptable Use Policy” their screen was taken over – and displayed “REPORT TO IT IMMEDIATELY!” That philosophy ensures compliance by extrinsic punishment – there is no intrinsic motivation to stay compliant. In my own way, I have changed our policy to that of “Mass Surveillance.” We track, record, monitor, and search all information on student computers and traffic through our servers. As a result, I get to see what the real danger of “Mass Surveillance” is. Teachers and Administrators have used the ability to search our surveillance logs in order to query students who are not connected to any current offense. Indiscriminate searching is common and done without any oversight.
So lets take my microcosm of 600 students monitored by approximately 20 staff members. In the NSA programs, 30 Million Americans are monitored by 90,000 NSA employees. At least we tell our students we are monitoring them… If we cannot ensure that 20 staff members will abide by privacy rules, how can the NSA with 2/3 of is workforce being private contractors, ensure that someone is not abusing the privilege of search.
The Arguments
The more I searched online, and the more I asked, I could only find two real reasons that people support Mass Surveillance. I do think that each of the issues is worth a discussion and we must look at the rationale behind why these arguments exist.
1) Mass Surveillance stops terrorists.
I do not doubt it for a minute! If you know what a terrorist is doing and can monitor his communications, you will be more able to stop him in the future (or for a slightly terrifying look at blowing up terrorist cellular phones – take a look at this). What I do not understand, and nobody has really discussed, is how stopping terrorism is a rationale for targeting 30 Million Americans. Offensive cyber security and defensive cyber security are not the same thing. We all understand weapons of war more than we should (and hopefully some of you know some SiFi) so let me explain this in a different way. The programs that were highlighted in the revelations about PRISM and X-Keyscore show that we are actively firing our cyber weapons at everyone all the time. Instead, we should spend our time working to shield ourselves from the offensive might of others. Can other nations use our own cellular phones as a weapon? Probably not. But we should prepare our defenses as though the can. As a people, we are really good at what we do. Stuxnet is a great example of American ingenuity. The German researcher at Sophos who worked on it listed its code as “Rocket Science.” If we can create such amazing and inspiring offensive weapons, perhaps we should look at how we protect ourselves from those same devices. At this point, we should not allow our government to use the tools of the War on Terrorism to wage war on its own population (which was echoed in the wake of Ferguson). That brings us to the second most prolific reason for supporting mass surveillance:
2) If you are not doing anything wrong you have nothing to hide.
I have done things that are wrong, and I want to hide them. I have terrible credit, and I am paying down a mountain of debt. The stunning change is what happens when what we do in private becomes public. Suppose that I like to dance around my house naked. What would happen if a video of me dancing found its way on to YouTube. I think a majority of people would laugh, but what about the parent of the 5 year old who stumbles across it? Or the person who has it emailed to them for a laugh? Who decides if you are doing something wrong? Is my monitoring of students a crime? What if the parents ask for it? What if the students oppose it? How about me dancing naked, is the a crime if I am being watched?
When you say that you do not care because you are not doing anything wrong… what you are really saying is that you accept the social norms of the group currently in Power.
What if the next President decides that a group you are a part of is illegal? Or in the previous case, makes dancing naked a crime? All of the sudden, you are doing something wrong! Would you care then?
**The dancing around naked was just an example, but if you want to hear from John Oliver about showing your Junk on the Internet, feel free.
What do we do?
After all of my research, and all of my time, there is really not much that we can actively do right now. It is up to each person to find an way to protect themselves and protect the freedom and privacy that we currently have. You can protect yourself and the future of the internet by promote and using companies committed to Zero-Knowledge Privacy. In the words of Edward Snowden:
“We need to code our values, not just in words, but in the structure of the internet.”
If you value freedom and privacy, as I do, there are a couple of things you can do:
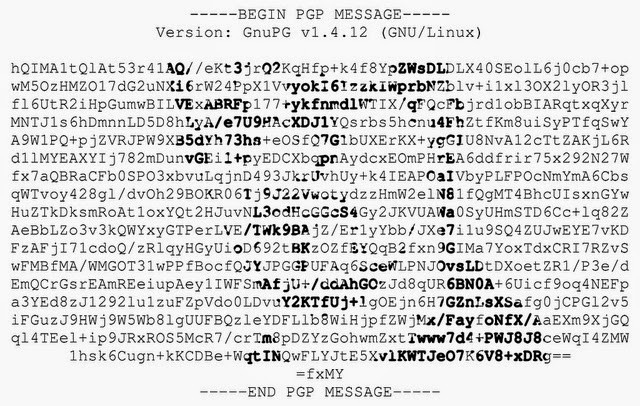
- Follow these companies: Silent Circle, Golden Frog, Kolab, LavaBoom, GitHub, etc.
- Follow the people listed in this Post.
- Learn and take action! Join the Electronic Frontiers Foundation, #UnFollowMe, Code For America, Privacy International, Amnesty, The Zero-Knowledge-Privacy Standard and all of the other wonderful organizations who protect our freedoms on a daily basis.
If you want help setting up your Zero-Knowledge system, stay tuned for more information.
